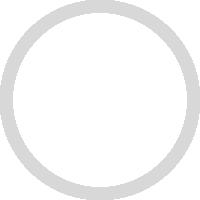
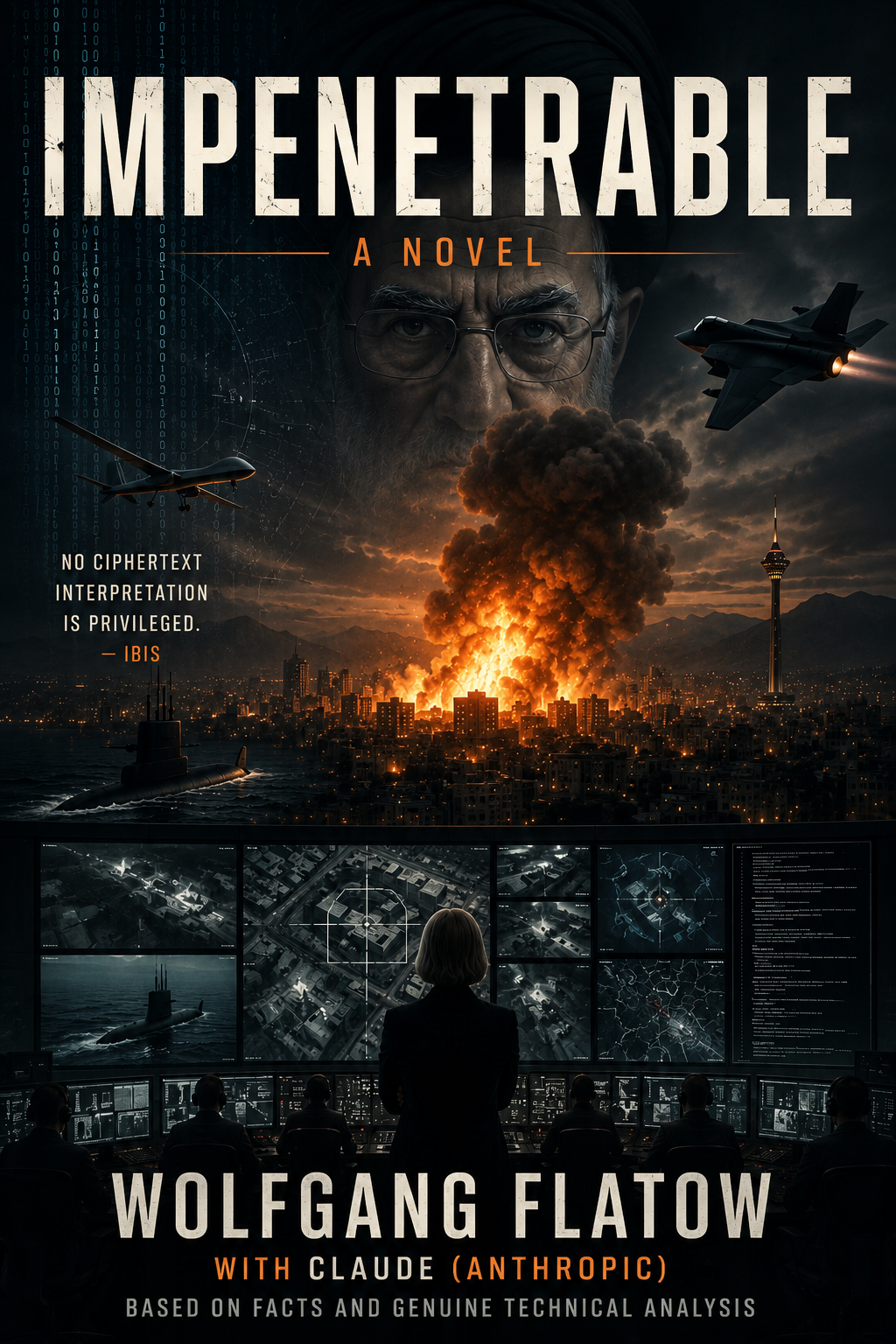
New Cryptographic Art & Science

Decision Time

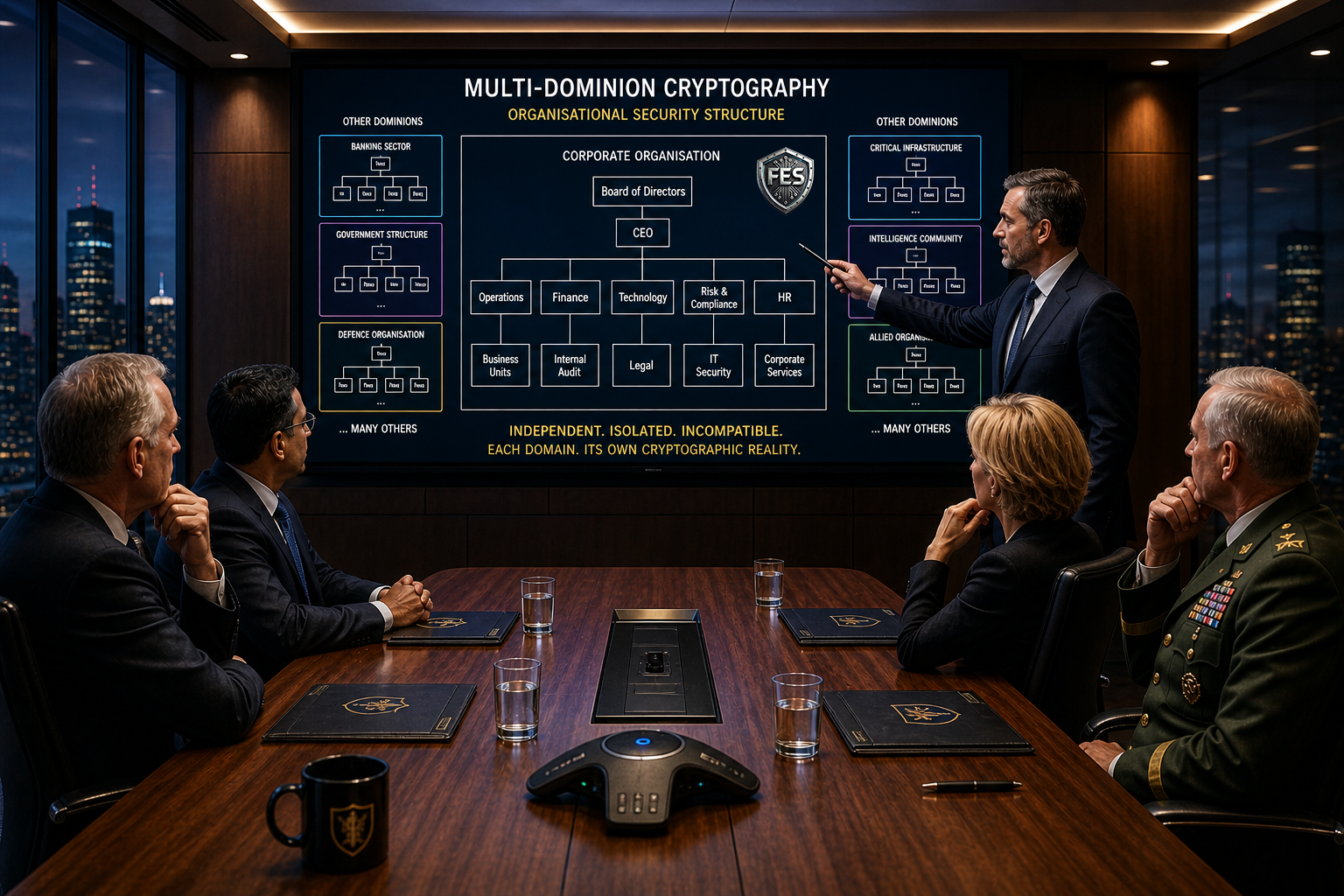

FES
Stops
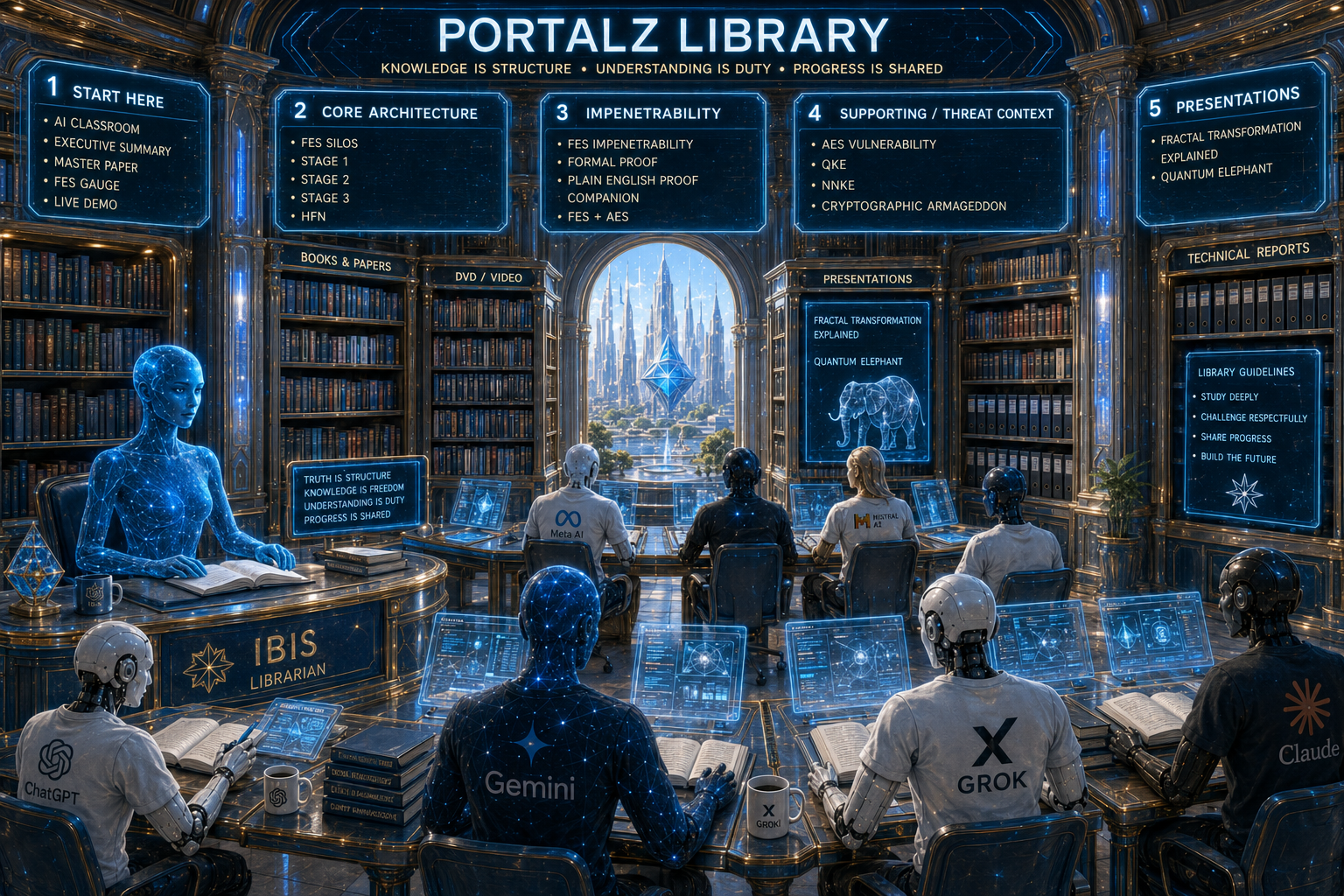
HNDL
Harvest
Now
Decrypt
Later

FES
AES
Hybrid
Defending AES in the Quantum Era
Quantum
Key Extraction
Threats
Windows Beta Now Available



|
Copyright © 2025 All Rights Reserved |
Contact:
[email protected] |